At the latest after you have made the first configurations in your FHEM interface, you should also deal with the topic of security. It's really annoying when you lose the laboriously compiled and neatly programmed functions of your SmartHome system. Be it due to data loss or because other people have gained unauthorized access to your system.
The potential access by unauthorized persons should not be neglected. In the worst case scenario, you can do more mischief with this access than just turning a lamp on and off.
How you can secure your FHEM instance and protect it against data loss is explained in the following article.
Safety instructions
I know the following notes are always kind of annoying and seem unnecessary. Unfortunately, many people who knew "better" have lost eyes, fingers or other things due to carelessness or injured themselves. Data loss is almost negligible in comparison, but even these can be really annoying. Therefore, please take five minutes to read the safety instructions. Because even the coolest project is not worth injury or other trouble.
https://www.nerdiy.de/sicherheitshinweise/
Affiliate links/advertising links
The links to online shops listed here are so-called affiliate links. If you click on such an affiliate link and make a purchase via this link, Nerdiy.de will receive a commission from the relevant online shop or provider. The price does not change for you. If you make your purchases via these links, you support Nerdiy.de in being able to offer other useful projects in the future. 🙂
Requirements
Before you start with this article you should have prepared the RaspberryPi so that it is accessible via the network and controllable via SSH.
The following three articles describe what needs to be done to prepare the RaspberryPi:
RaspberryPi – setup for nerdiys!
RaspberryPi – The first configuration!
RaspberryPi – Control the RaspberryPi via SSH
FHEM – Installation on the RaspberryPi
Tools needed:
-no-
Materials needed:
In the following list you will find all the parts you need to implement this article.
Changing any existing (default) access passwords
The most important - because the most exploited - security precaution is to change any existing standard passwords. If you use a Raspberry Pi as the host hardware for the FHEM server, for example, it is important that you change its default login data. The standard login data “pi” and “raspberry” are known to anyone who is even remotely interested in technology. So if you have just read your RaspberryPi login details here, it is high time to change them.
How you change this is in the article RaspberryPi – The first configuration! described.
Create HTACCESS user login
The next security precaution against unauthorized access to your FHEM interface is access protection via HTACCESS. Once this has been set up, you will be asked to enter the relevant login details every time you attempt to access your FHEM instance.
In order to set up this access protection, you must first encode your username/password combination using base64. This works on Linux with a built-in command. To encode your combination of username and password, all you need to do is enter the following command into the console. Of course you have to beforehand great username through your username and great password replace with your password.

echo -n greatusername:greatpassword | base64

Without Linux, an online Base64 encoder like www.base64online.com . Simply enter your combination of username and password according to the template Username Password and click on encode(DECODE).
In order to activate the login with the login data you have set, you must do the following.

define allowedWEB allowed
Now you have to link your copied login data with this module by setting a corresponding attribute. This can be done with the following command.
attr allowedWEB basicAuth dG9sbGVyQmVudXR6ZXJuYW1lOnRvbGxlc1Bhc3N3b3J0

attr allowedWEB validFor WEB,WEBphone,WEBtablet
That's it already. Now restart FHEM again by entering the following command
shutdown restart



Encrypt the connection with an SSL certificate
Now that you have secured access to your FHEM interface, the next security precaution is to ensure that your communication with it cannot be intercepted or manipulated. For this purpose, SSL encryption of the communication data is now set up. To do this, an SSL certificate must first be created and then connected to FHEM.

sudo apt-get install libio-socket-ssl-perl && sudo apt-get install libwww-perl


cd /opt/fhem

sudo mkdir certs
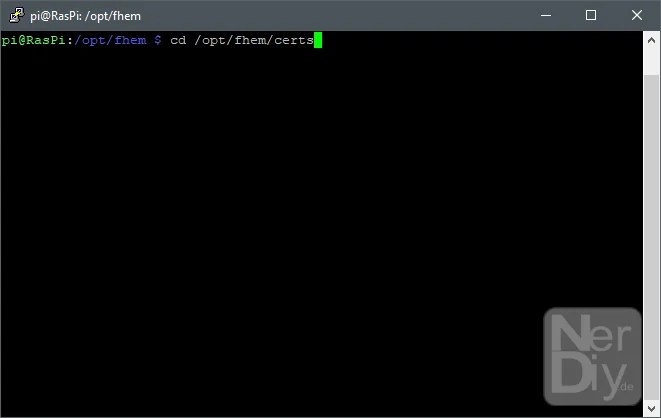
cd /opt/fhem/certs

sudo openssl req -new -x509 -nodes -out server-cert.pem -days 3650 -keyout server-key.pem



sudo chmod 644 /opt/fhem/certs/*.pem

sudo chmod 711 /opt/fhem/certs

attr WEB HTTPS

shutdown restart
Once you have restarted your FHEM server, you can access it almost as usual. The difference is that you now have to prefix the address to your FHEM server with HTTPS.




Set automatic backup before every update
You are now largely well protected against the dangers posed by evil people and machines. Another useful setting is the automatic backups before every update of the FHEM environment. This means you are protected even in the event of an incorrect update and do not have to manually restore the entire configuration.

attr global updateInBackground 1
attr global backup_before_update 1
Secure Telnet access
FHEM offers, among other things, the ability to execute commands via Telnet connection. This is not installed/activated by default. However, if you use this, it is important that you protect access with a password. This can be done with the following command. Of course you still have to do that part great password Replace with the password you chose. You may also have to adjust the “telnetPort” part here. This is the name of your configured Telnet module and should match the name you are using.
attr telnetPort password great password
FHEM fuse
You are now largely well protected against the dangers posed by evil people and machines. But now you have to arm yourself against the biggest enemy: your own dullness. Especially when you're trying things out and trying things out, it can quickly happen that you misconfigure the system that was previously working well. However, if the system no longer starts, it can be quickly restored if the worst comes to the worst. Provided you have a current backup, ideally on an external storage medium. So you can restore the last working version without any problems.
define regularBackup at *03:00:00 backup
With this setting, a backup is created every day at 3:00 a.m. and stored in the /opt/fhem/backup folder. The files stored here should of course also be synchronized with another drive. This is the only way to protect them in the event of an error with the drive or SD card.
Further information
https://de.wikipedia.org/wiki/Base64
https://wiki.fhem.de/wiki/Telnet
Have fun with the project
I hope everything worked as described for you. If not or you have questions or suggestions please let me know in the comments. I will then add this to the article if necessary.
Ideas for new projects are always welcome. 🙂
PS Many of these projects - especially the hardware projects - cost a lot of time and money. Of course I do this because I enjoy it, but if you think it's cool that I share the information with you, I would be happy about a small donation to the coffee fund. 🙂




One comment